LDRA
Suite 228
Lewisville, Texas 75056 [email protected]
(855) 855 5372
https://ldra.com/

LDRA Develops Multi-Core Analysis Capabilities to Detect and Ease Timing Coupling Interference - News
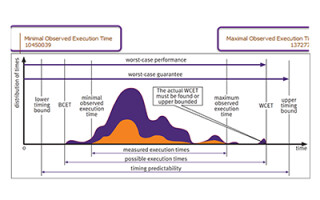
November 13, 2025Wirral, United Kingdom. LDRA announced that its LDRA tool suite now supports enhanced analysis of timing coupling interference on multi-core architectures. Building on previous data coupling and control coupling tools, the new abilities present designers further insight into multi-core performance while allowing them to mitigate timing issues.
Avoiding Potential Software Bugs with MISRA C:2025 - Blog
June 10, 2025Whether they are caused by accident or a mistake, bugs are a critical part of developing software for embedded systems. And when those systems must be safe, secure, and reliable – think applications like aerospace, automotive, defense, energy, industrial, and medical – developers need tools to help them assure they’ve covered all the bases before software is deployed.
LDRA Enhances Renesas Ecosystem with Seamless Functional Safety and Cybersecurity Verification - News
June 09, 2025Wirral, United Kingdom. LDRA publicized it joined both the Renesas Ready Partner Network and the R-Car Consortium. The relationship extends LDRA's support to seamlessly incorporate system development tools utilizing Renesas R-Car system on a chip (SoCs), microprocessors (MPUs), and microcontrollers (MCUs) that are required to be in full compliance with industry-wide functional safety and cybersecurity standards.
Designing for Safety and Reliability in Multicore Hard-Real Time Applications - Blog
June 03, 2025Hard real-time applications, including automotive, avionics, industrial, and military systems, demand deterministic execution times for mission-critical tasks. To increase performance, many of these applications utilize multicore processors to split complex software code across many cores to reduce overall processing execution time.
Industrial
Ken Briodagh Interviews Jim McElroy with LDRA at embedded world 2025 - Video
April 28, 2025Watch now.
Tech News Roundup
ICYMI: Embedded Insights Episode 6 - Video
February 28, 2025Hello Embedded Engineers, Developers and Makers! Welcome to In Case You Missed it: Embedded Insights, the weekly news show all about Embedded technologies and solutions from Embedded Computing Design.
Transforming Modern Manufacturing: Robotics, Automation & Functional Safety - Podcast
February 27, 2025In this episode of Embedded Insiders, Winston Leung, Senior Product Marketing Manager at QNX, and Jay Thomas, Director of Field Development at LDRA join the podcast to discuss the fusion of robotics and automation in modern manufacturing, and how functional safety is shaping this transformative shift.