ETSI’s Problem with Encrypted Network Traffic
August 26, 2022
Story

Everyone knows encryption is a cornerstone of network security, but at this point very few understand what a problem it is.
According to ETSI, we’re all about to find out.
Last year ETSI released the GR ETI 001 problem statement on Encrypted Traffic Integration (ETI), which identifies and attempts to address the challenges our own security mechanisms pose in an increasingly connected world. Specifically, the document outlines the negative impacts of encrypted traffic on third parties attempting to access content who don’t have access to encryption keys.
While you may be thinking that’s exactly the point of encryption, consider that we now live in a world of technologies built on the interdependence of applications, data, and ubiquitous connectivity. For example, a single DoorDash order requires that data traffic is shared between a customer, the DoorDash platform, the restaurant, and a delivery driver, all of whom must be able to access order information in a secure but transparent fashion.
The ETSI GR ETI 001 problem statement focuses on a phenomenon called “Going Dark,” or the inability of an authorized, indirect party like a service provider or network operator to access network communications as a result of pervasive, end-to-end traffic encryption. As you can imagine, this is a mounting problem as more connected IoT devices and services come online.
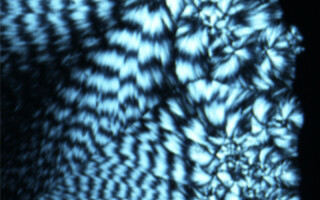
For example, the Venn diagram below illustrates how encrypted content and headers can result in blind spots for connected endeavors. Where A represents the need for openness and network transparency, B represents fundamental technology requirements of connected enterprises (including security), and C depicts regulatory obligations like EU GDPR/Cybersecurity Act, Radio Equipment Directive, and ePrivacy Regulation.

Figure 1: Representation of encrypted content that results in Going Dark (ETSI)
Between the three circles, communications can go dark. ETSI refers to these intersections as “limitations on networks.” This challenge applies to simplified network models, layer obfuscation in architectures like VPNs, and of course stakeholder models. For instance:
- Simplified Network Model: In some cases the packet payload may need to be examined to validate packet header contents that describe how it should perform at N network layer. Encryption would only allow peers with the key to verify the header against the packet payload.
- Layer Obfuscation Model: Layering packets and encryption like Russian nesting dolls creates a similar issue as above by requiring that stakeholders who need access to inner-layer packets have encryption keys to all layers above and including the one they need to access.
- Stakeholder Model: As described throughout, the different types of users – non-adversarial or network managers – may need, but not have access to, encryption keys that reveal required packets and data.
Building Transparent Security through ETSI’s ISG ETI
As the Venn diagram illustrates, “Going Dark” is a technical problem without an obvious solution. For example, how can authorities access data protected by privacy regulations like images, which would require access to at least N+1 layers of the network and subsequently some type of encryption override capability?
To address this gap, ETSI announced the continuation of its Industry Specification Group Encrypted Traffic Integration (ISG ETI) to mid-2024 to help thread stakeholder access with ubiquitous encryption. For the purposes of the ISG ETI, encryption also includes integrity and trust principles.
The ISG ETI will work towards cryptographic and key management models that provide all stakeholders with appropriate levels of access across the communications chain to meet the requirements of various application domains like eHealth, Intelligent Transportation, and Smart Cities. These solutions will be considered in the context of regulatory and legislative to “ensure that the ‘trust contract’ and ‘zero trust model’ are feasible in deployed networks.”
The ETSI working groups involved in the ISG ETI include:
- CYBER
- Lawful Interception
- Network Function Virtualization
- Fifth-generation fixed network (F5G)
Today, ISG ETI working group members include major mobile carriers like AT&T, T-Mobile, and TELEFONICA, and network equipment manufacturers Huawei Technologies, Palo Alto Networks, Netscout Systems, etc. However, the ways this will impact IoT device traffic in the near future can’t be overstated.
To learn more and get involved, read the 2021 ISG ETI Activity Report at https://www.etsi.org/committee-activity/activity-report-eti, go to the ETI wiki at https://etiwiki.etsi.org/index.php?title=Main_Page, or view the group’s current work items and statuses at https://portal.etsi.org/tb.aspx?tbid=888&SubTB=888#/.