How TPM 2.0 Enables Foundational Security in Rugged Edge Computers
April 22, 2020
Story

Trusted platform module (TPM) is one of the most prominent security platforms that is based on the IEEE 802.1x authentication framework and can be integrated into low-power edge computing designs.
A plethora of security technologies has emerged to serve the Internet of Things (IoT) and other embedded system designs over the years. Trusted platform module (TPM) is one of the most prominent security platforms that is based on the IEEE 802.1x authentication framework and can be easily integrated into low-power edge computing designs.
However, before delving into why are edge computers specifically integrating TPMs into their hardware, it’s important to understand how this security technology works. TPMs, implemented by either soldering a security chip onto PCB or by integrating TPM functionality into a chipset, provide hardware-based security to enforces device authentication via unique, unalterable root key that is burned into the chip. It enables secure generation and storage of cryptographic keys to safeguard information in resource-constrained IoT devices.

Figure 1: An overview of security features and capabilities that TPMs bring to edge computers. Image: Premio
In a TPM solution, the root key encrypts other encryption keys produced by other applications and these keys from an extra layer of protection by encrypting files, folders, and drives. That enables embedded system designers to create robust data protection at a time when the number of data privacy controls are multiplying.
The data privacy controls such as GDPR, HIPAA, and PCI-DSS cover both personally identifiable information (PII) and protected health information (PHI) to prevent the mishandling of information in connected devices. GDPR alone has been responsible for half a billion dollars in penalties to some of the biggest corporations.
Another reason for the prevalent use of TPM in embedded designs, especially low-power edge computers, is the availability of TPM 2.0 solutions that address the modern-day security threats in embedded systems.
TPM 2.0 security features
The security module first standardized in 2009 has evolved from the original TPM 1.2 version to adapt to the recent advancements in compute processing. The TPM 2.0 standard implements several new features, including algorithm interchangeability instead of reliance on a single hash algorithm, SHA-1, and enhanced signature data to allow verification support for PINs, biometrics, and GPS data.
Next, the addition of password authentication bypasses the implementation of authentication software in applications calling for lower levels of protection, and this feature flexibility goes a long way in resource-constrained IoT designs. There are also improvements in key management so that authentication keys can be delegated for limited or conditional use.
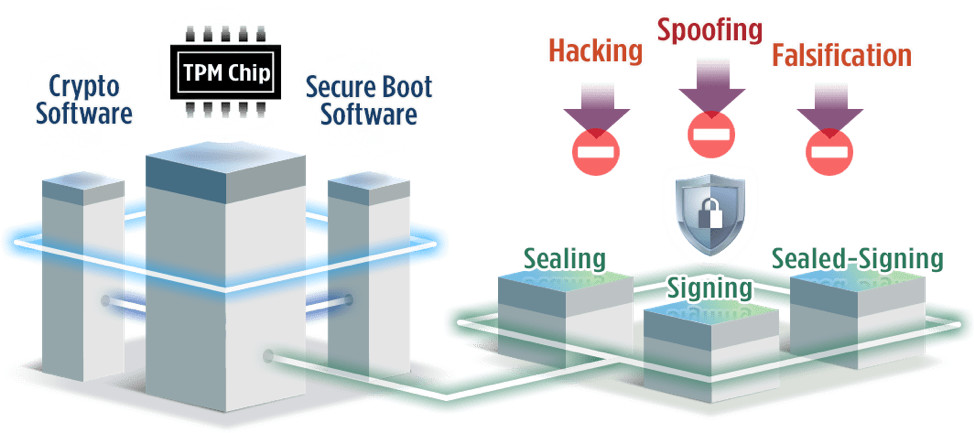
Figure 2: The three hierarchies in TPM 2.0 permit multiple root keys to boost protection against malware and other rogue attacks on edge computers. Image: Premio
These security features are going to be crucial in edge devices that are now facing the brute force of hacking attempts. The unmonitored devices at remote locations, for instance, need to be protected from unauthorized parties installing malware. That can corrupt or exfiltrate data, or it can be used to manipulate the system.
Take the example of connected surveillance systems, where along with videos and images, there is a lot of accompanying information that can be leaked or breached in the absence of adequate encryption. Likewise, biometrics data from facial recognition scanners or financial data tied to point-of-sale (PoS) kiosks or banking surveillance services can be compromised, leading to severe penalties for public and private organizations.
TPM 2.0 on rugged edge
The above example demonstrates the need for the TPM technology to ensure that data is encrypted from connected devices to the edge to the cloud. It’s even more vital in industrial and mission-critical infrastructure where data breaches and unauthorized system access can have catastrophic results.
The data leaked or breached from edge devices could lead to violations of privacy controls like GDPR, CCPA and HIPAA, resulting in severe financial penalties, draining lawsuits and harm to company reputation. For manufacturing and critical infrastructure, the STUXNET worm demonstrated the physical toll that successfully installed malware can take on operational technology (OT) and cyber-physical systems. TPM technology can halt the few lines of rogue code capable of manipulating machinery, valves and sensors that can cause injury to humans, as well as extensive damage to equipment and catastrophic environmental destruction.
Premio’s rugged edge computers incorporate the TPM 2.0 module on motherboards to employ critical hardware security encryptions. This security protection is easily enabled in the BIOS of the computer and can be toggled on for remote edge deployments. Another distinct feature that Premio’s rugged edge computers offer is the scalable GigE network modules that provide up to x18 Ethernet connections (x2 onboard / x4 quad-port modules). These plug-and-play modules are based on two Intel Ethernet controllers, the i210 and i350, a common network controller from Intel and are also offered in m12 locking connectors applications that experience shock and vibrations. Both of these Ethernet controllers help facilitate basic building blocks for multiple standard 1000Base-T interfaces (IEEE 802.3ab standard) in compact rugged edge computers.
These upgradable network modules support both LAN and Power-over-Ethernet (PoE) devices, but the i350 chipset version specifically enables security checks that display what’s happening on both inbound and outbound traffic. The PoE connections allow surveillance cameras, access control systems, and security alarm systems to be strategically placed without any restrictions of available resources due to its single cable design for power and connectivity.
Another merit of this TPM-based solution is that, while being a hardware security anchor, it explores the security features built at the operating system (OS) level to boost the chain of trust for the edge computers.
TPM’s foundational security
Finally, when embedded system designers move to the OS layer, Microsoft Windows 10 IoT features an entire suite of security features that can be built on top of the security-enabled hardware and firmware. Windows 10 IoT has made a big push in the security realm by creating a ton of features on top of the operating system, and these features are factored into the TPM module.
That also shows how TPM built into edge computers provides the security foundation that serves numerous critical functions. Especially, for rugged edge computers that are often deployed in areas that are not regularly monitored, so they are susceptible to tampering because of their remote deployment. The foundational security provided by TPM ensures that these rugged edge computers behave in a certain way, or they don’t behave at all.