The Multiple Dimensions of Embedded & IoT Security
December 21, 2018
Blog
Everyone knows embedded and IoT security is important. But when drilling down beyond the initial head-nod agreement, the interpretation of what security is elicits vague and varied responses.
Everyone knows embedded and IoT security is important. But when drilling down beyond the initial head-nod agreement of its importance, the interpretation of what security is and how to test for it elicits vague and varied responses. In this article, Dr. Markus Kammerstetter of Trustworks KG talks about the many dimensions of Embedded and IoT security.
Security Expertise in Unexpected Places
Vienna, Austria is thought of as a leader in the renaissance period with rich talent in music and the arts. Perhaps not so ironically, in the heart of Vienna lies Trustworks KG, a company focused and experienced with the many facets of securing and exposing vulnerabilities in a variety of systems and industries.
It all started in 2005 when Dr. Kammerstetter was working on his master degree in security at the Technical University of Vienna while also working as a security consultant for enterprise systems and products. This is where he began gaining experience and developing tools to identify security vulnerabilities working with software binaries since his customers were the users, not the product companies where source code is available.
In 2007 Markus started to invest in hardware security analysis tools like microscopes, probe stations, wet chemical etching equipment. In 2012 things grew to the point where Trustworks the company was born. In the years following, he began to assemble a team where all have a very strong security background. Markus describes himself and his team as “tinkerers” – they love to work with electronics, design schematics & PCBs. In addition to that they have a strong background in security. Combining a well founded security education, practical experience and the strong interest in electronics and microchips results in a unique embedded security expertise.
In 2016 Markus completed his PhD in Emebdded Security. Likewise, his employees are also connected to the university pursuing their masters and PhDs in Security.
Embedded Security
Most of the time you can work with less sophisticated tools – firmware disassemblers, fuzz testing tools, protocol testers, maker boards, programming tools, or other things that can be used to conduct security testing. They also have a goal to not just provide security testing, but they are also constantly expanding their capabilities, performing independent security research, and publishing their results.
Over time, they have built up an impressive set of software, firmware, and hardware tools, techniques, and capabilities for broad-based security and vulnerability testing. An example of their prowess includes an initiative they undertook to develop an high performance FPGA based Wi-Fi WPA2 implementation in order to test for weak keys or a software tool than can extract netlist information from high resolution microchip images.
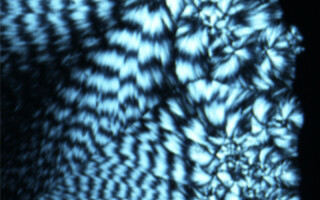
Figure 1 shows a Microscope that has been augmented with home-made circuit boards and open source software to perform chip analysis. They actually used a game controller to provide fine-grain movement and switch to slow motion to get the image in focus. This in conjunction with custom software addons to the Micro Manager open source software, they can control the stage, read the image from the camera, and Micro manager has different autofocus or automated image acquisition where they can put a grid over the chip and the software can figure out how many pictures to take. Then these pictures can be stitched together with their own software tools to get a picture of the entire chip. For high resolution chip imaging, they use the same software setup with a Scanning Electron Microscope (SEM).
All of these hardware tools and analysis capabilities provide a robust environment for analyzing product security from a product, board, chip, and software perspective.
Figure 2. Plasma Etching machine for IC Delayering
Figure 2 shows a Plasma Etching machine where, combined wth other methods, they can carefully remove microchip layers for subsequent microscopic image analysis to perform security testing.
Views on IoT and Embedded Security
The eye opening revelation for me talking through the equipment and product/board/chip decomposition capabilities of Trustworks is that security isn’t just focused on whether someone can guess a password or inject viruses or gain access through the software. There are a lot of on-chip security features these systems depend on. Trustworks and their security capabilities dissect these features and analyze them for a comprehensive chip-to-software-to-product security analysis.
Markus also commented on the uniquenesses of IoT systems and how it’s not just the IoT device vulnerability, but the cloud infrastructure security can be equally dangerous.
Building Security Into Legacy Systems Turning “Smart”:
Markus also cautioned that special attention be paid to established products and capabilities from larger companies where they are attempting to migrate existing products to “smart” products. There can be significant security challenges migrating existing products with established designs, chips, and software that developing from scratch doesn’t have to worry about. This often results in short-cuts that work with legacy chips or software where the new “smart” part is secure, but the vulnerabilities in the legacy components are still there. Markus also mentioned the embedded and IoT companies are making the same mistakes made by enterprise companies years ago.
A common security practice involves using encryption. While Markus applauds the use of encryption, the correct implementation and application of cryptography is not always easy and implementation flaws could mitigate any security gained. For example, how are your keys generated? How do you exchange keys with other devices? How do you store it? How do you protect it from read-out? Does each device has its own keys or do they share the same key?
Markus cited an analysis done by security researchers of a car manufacturer of makes and models over a ten year period [1]. They analyzed the car keys and understood how the keys worked in general. They performed side channel attacks and performed the analysis to extract the cryptographic keys used. They found out that the manufacturer used only a few individual keys for all the car keys of all the models. If you know those keys, then you can unlock essentially every make and model of car. This is one of those fails where you might have established cryptographic algorithms, but your keys are the weakness.
Summary
Security is serious business and the stakes are becoming even higher with IoT and smart, connected embedded products. Starting with security in mind, performing product, board, circuit, and software security audits, and making sure the application of the security features don’t in and of themselves cause security issues are the key takeaways from my visit to Trustworks.
References:
[1] https://assets.documentcloud.org/documents/3010178/Volkswagen-amp-HiTag2-Keyless-Entry-System.pdf